SIPVicious (Auditing SIP Based VoIP System) :: Tools - ToolWar | Information Security (InfoSec) Tools
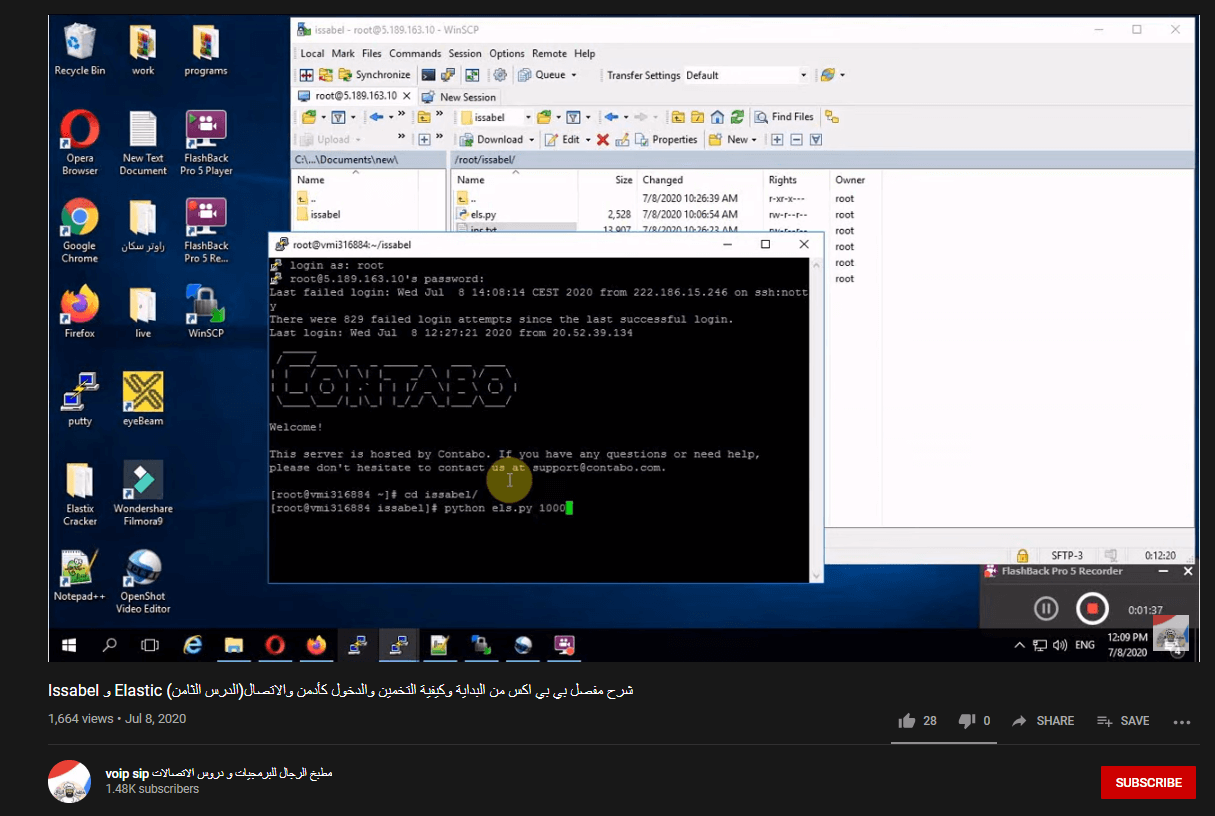
Who's Calling? Gaza and West-Bank Hackers Exploit and Monetize Corporate VoIP Phone System Vulnerability Internationally - Check Point Software


![kamailio:usage:k31-sip-scanning-attack [Asipto - SIP and VoIP Knowledge Base Site] kamailio:usage:k31-sip-scanning-attack [Asipto - SIP and VoIP Knowledge Base Site]](https://kb.asipto.com/lib/exe/fetch.php?tok=0103dd&media=http%3A%2F%2Fkb.asipto.com%2Fimages%2Fvu-attack%2Fssattack-shmem.png)



![How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub](https://packt-type-cloud.s3.amazonaws.com/uploads/sites/2432/2018/06/d91128ab-48ff-4568-9a18-508976447fba.png)





![How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub](https://packt-type-cloud.s3.amazonaws.com/uploads/sites/2432/2018/06/b24418b9-270a-4f66-bea4-61add03ce088.png)
![kamailio:usage:k31-sip-scanning-attack [Asipto - SIP and VoIP Knowledge Base Site] kamailio:usage:k31-sip-scanning-attack [Asipto - SIP and VoIP Knowledge Base Site]](https://kb.asipto.com/lib/exe/fetch.php?tok=fae3dc&media=http%3A%2F%2Fkb.asipto.com%2Fimages%2Fvu-attack%2Fssattack-rcvreqs.png)

![Registration hijacking process on SIP based IP network[11] | Download Scientific Diagram Registration hijacking process on SIP based IP network[11] | Download Scientific Diagram](https://www.researchgate.net/profile/Smarajit-Ghosh/publication/266072428/figure/fig3/AS:315319156527106@1452189353442/Registration-hijacking-process-on-SIP-based-IP-network11.png)
