Shodan founder John Matherly on IoT security, dual-purpose hacking tools, and information overload | The Daily Swig
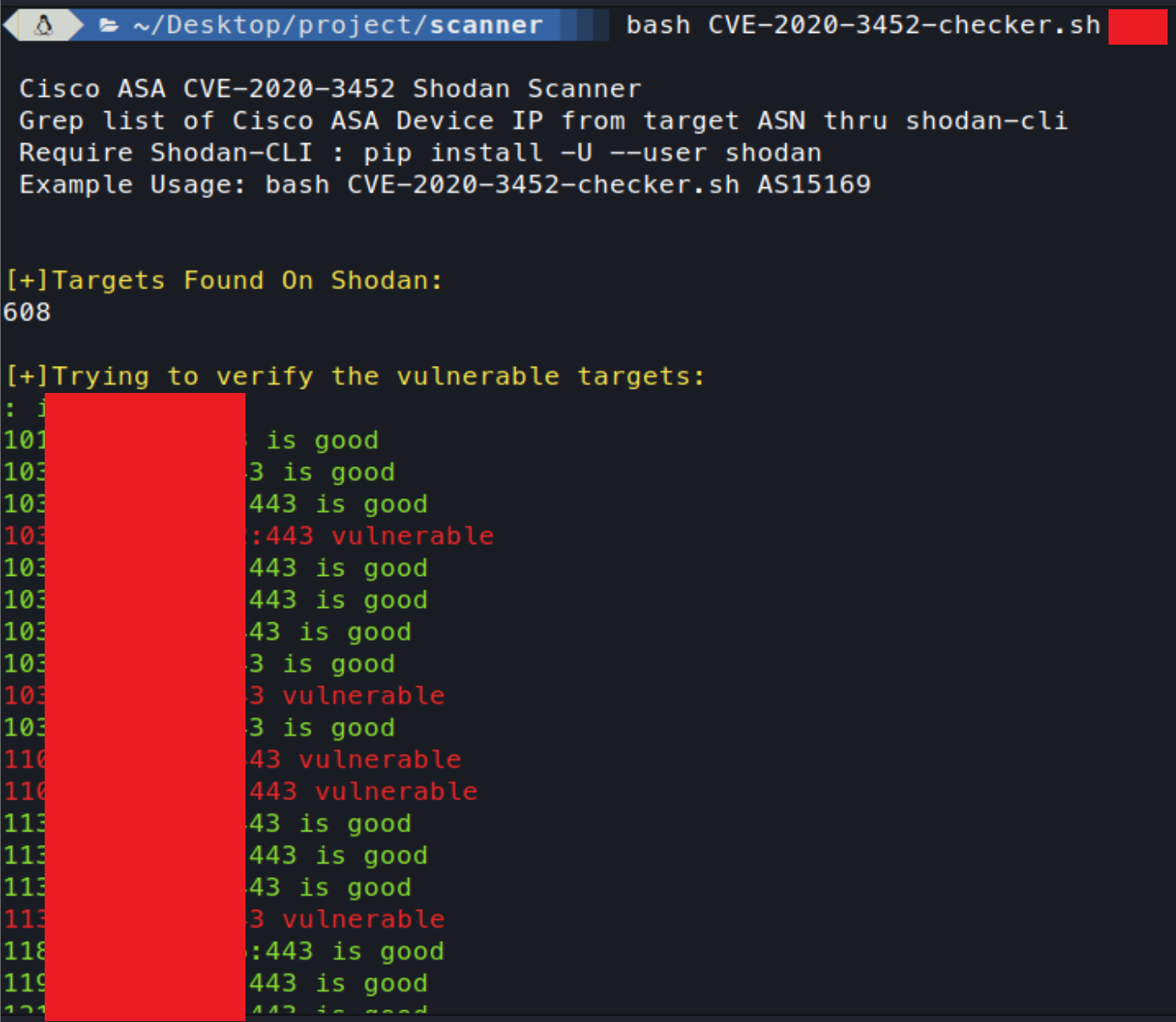
GitHub - faisalfs10x/Cisco-CVE-2020-3452-shodan-scanner: simple bash script of CVE-2020-3452 Cisco ASA / Firepower Read-Only Path Traversal Vulnerability checker
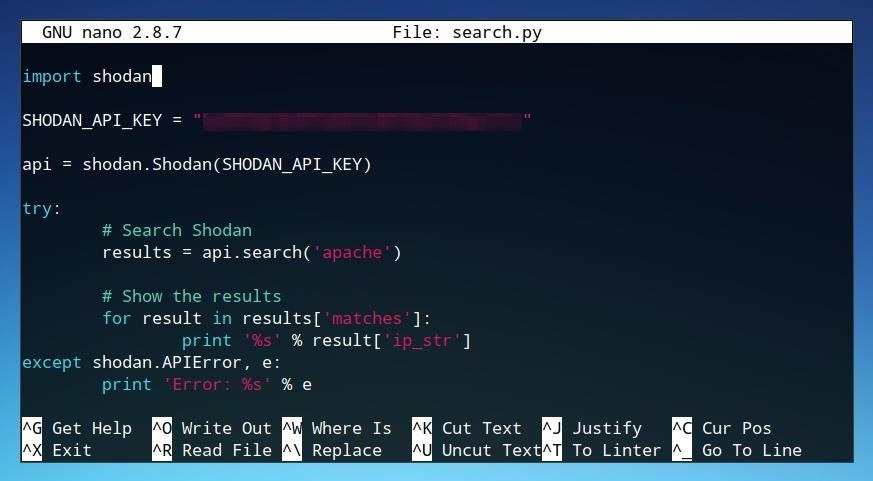
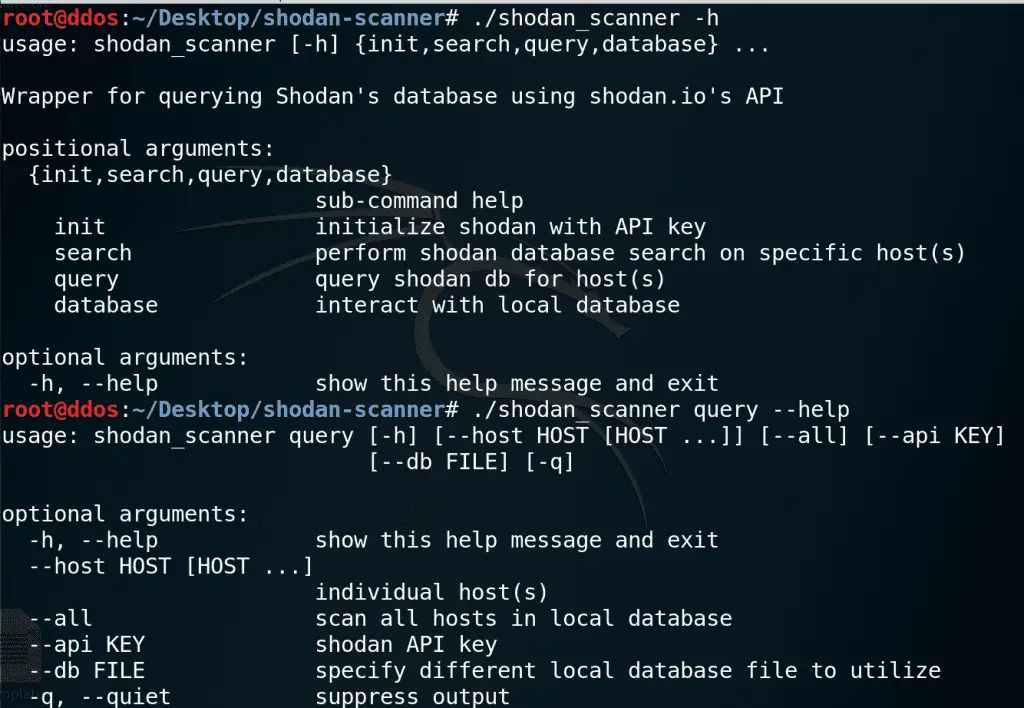
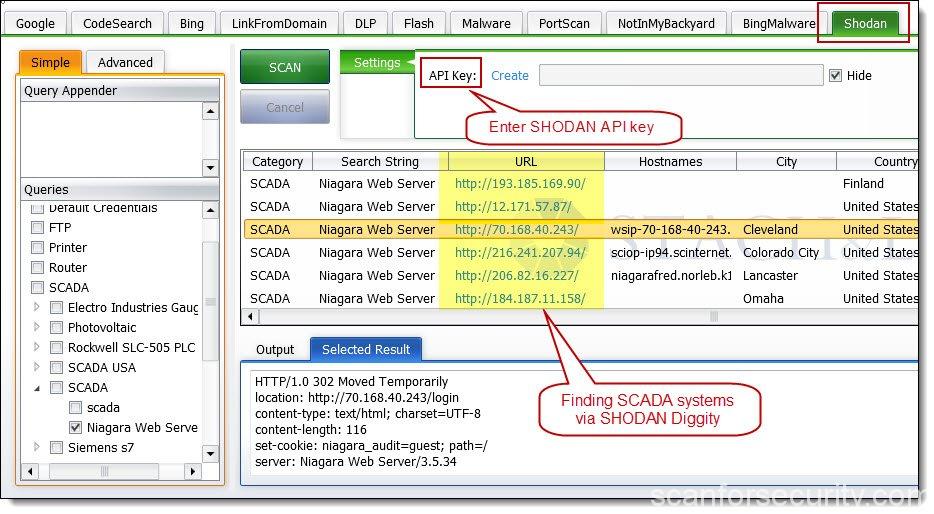
The Hacks of Mr. Robot: How to Use the Shodan API with Python to Automate Scans for Vulnerable Devices « Null Byte :: WonderHowTo



![What Is Shodan? How to Use It & How to Stay Protected [2022] What Is Shodan? How to Use It & How to Stay Protected [2022]](https://static.safetydetectives.com/wp-content/uploads/2019/06/What-is-Shodan-and-how-to-use-it-Most_Effectively.jpg)
![Smap: Alternate Network Scanner of Nmap by shodan.io [Examples] - TREND OCEANS Smap: Alternate Network Scanner of Nmap by shodan.io [Examples] - TREND OCEANS](https://trendoceans.com/wp-content/uploads/2022/04/Thumb-Nail-66-compressed.jpg)

![Shodan Command Line a Step by Step Walkthrough - HackingPassion.com : root@HackingPassion.com-[~] Shodan Command Line a Step by Step Walkthrough - HackingPassion.com : root@HackingPassion.com-[~]](https://hackingpassion.com/shodan-command-line-a-step-by-step-walkthrough/featured-image.png)